Anonforce
Anonforce is a TryHackMe machine that focuses on FTP misconfiguration, PGP encryption, and password cracking. The box exposes an FTP server with anonymous login enabled, granting access to the entire
Search for a command to run...
Articles tagged with #hashing
Anonforce is a TryHackMe machine that focuses on FTP misconfiguration, PGP encryption, and password cracking. The box exposes an FTP server with anonymous login enabled, granting access to the entire
Website defacement is one of the more visible outcomes of a successful cyberattack, and investigating one end-to-end is a great way to practice mapping attacker behavior across the full Cyber Kill Cha

Key Terms Before we start, we need to get some jargon out of the way.Read these, and take in as much as you can. We'll expand on some of them later in the room. Plaintext - Data before encryption or h

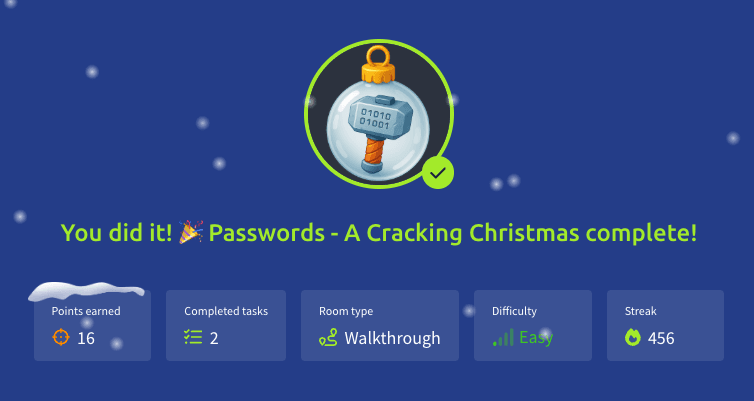
This challenge drops us back into the shifting world between Easter and Christmas, where the once‑stable systems of The Best Festival Company begin behaving strangely. Hidden deep within the servers, Sir Carrotbane stumbles upon a collection of encry...
In this task, we explore the fundamentals of enumeration, exploitation, and privilege escalation on a vulnerable machine. By leveraging tools like Nmap, Gobuster, cURL, John the Ripper, and Steghide, we methodically uncover hidden directories, decode...
In this article, we’ll cover Hash cracking - You wanna know what happens to your hashes? write-up as the Day 23 challenge of the Advent of Cyber event challenge. It involved hash functions and hash values, saving hashed passwords, cracking hashes, an...