Introduction to Offensive Security: Network Security (TryHackMe)
In this article, I will write a write-up for Network Security that covers Methodology and Practical Examples of Network Security.
What type of firewall is Windows Defender Firewall?
Host FirewallDuring which step of the Cyber Kill Chain does the attacker gather information about the target?
ReconLet’s summarize what we have done in this task to get
rootaccess on the target system of IP addressMACHINE_IP:We used
nmapto learn about the running services.We connected to the FTP server to learn more about its configuration.
We discovered a file containing the root password mistakenly copied to a public folder.
We used the password we found, allowing us to log in successfully.
We gained access to all the users’ files.
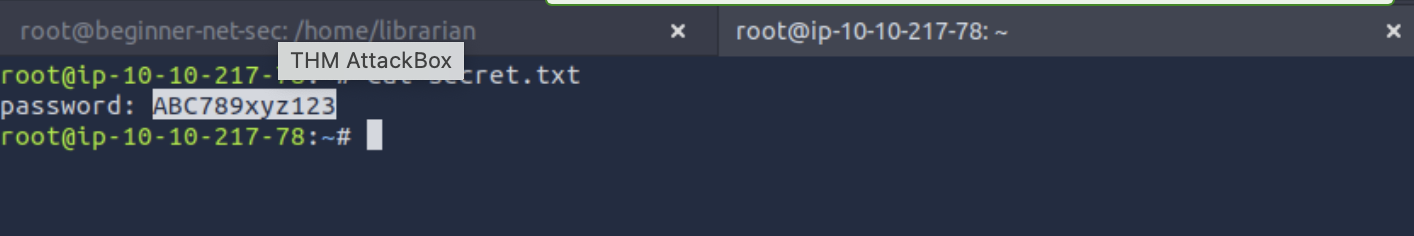
What is the password in the
secret.txtfile?ABC789xyz123
What is the content of the
flag.txtin the/rootdirectory?THM{FTP_SERVER_OWNED}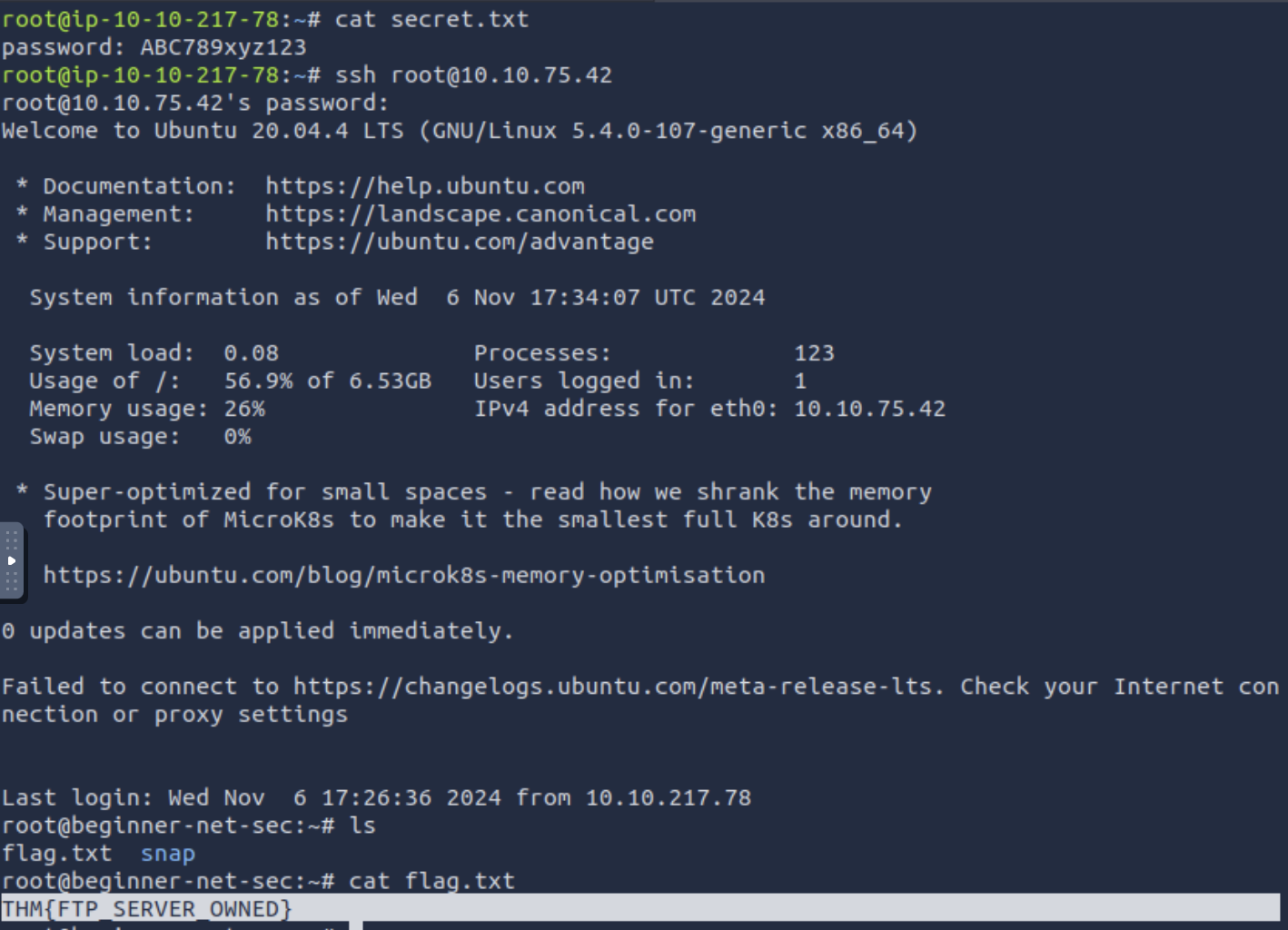
What is the content of the
flag.txtin the/home/librariandirectory?THM{LIBRARIAN_ACCOUNT_COMPROMISED}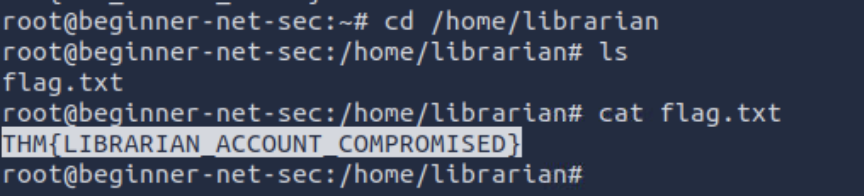
Thank you for reading my article. Please leave any questions or comments on improving my learning journey and the Lab THM challenges.




