Hidden Deep Into my Heart - Information Disclosure (TryHackMe)
Hidden Deep Into My Heart is a web application information disclosure Challenge that was part of the Love at First Breach 2026, red team beginner’s CTF. It covers:
web enumeration
broken authentication (OWASP A07:2021) through weak credential management:
hardcoded passwords
default/predictable usernames
No rate limiting or additional security measures
security misconfiguration(OWASP A05:2021):
Improper use of robots.txt
Credentials in comments
Admin panel exposed on public-facing server
My Dearest Hacker,
Cupid's Vault was designed to protect secrets meant to stay hidden forever. Unfortunately, Cupid underestimated how determined attackers can be.
Intelligence indicates that Cupid may have unintentionally left vulnerabilities in the system. With the holiday deadline approaching, you've been tasked with uncovering what's hidden inside the vault before it's too late.
You can find the web application here:
http://MACHINE_IP:5000
nmap -p- -sV <IP_Address>
Starting Nmap 7.80 ( https://nmap.org ) at 2026-02-14 10:06 GMT
mass_dns: warning: Unable to open /etc/resolv.conf. Try using --system-dns or specify valid servers with --dns-servers
mass_dns: warning: Unable to determine any DNS servers. Reverse DNS is disabled. Try using --system-dns or specify valid servers with --dns-servers
Nmap scan report for 10.48.130.4
Host is up (0.00012s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
5000/tcp open upnp?
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port5000-TCP:V=7.80%I=7%D=2/14%Time=69904931%P=x86_64-pc-linux-gnu%r(Ge
SF:tRequest,607,"HTTP/1\.1\x20200\x20OK\r\nServer:\x20Werkzeug/3\.1\.5\x20
SF:Python/3\.10\.12\r\nDate:\x20Sat,\x2014\x20Feb\x202026\x2010:06:40\x20G
SF:MT\r\nContent-Type:\x20text/html;\x20charset=utf-8\r\nContent-Length:\x
SF:201367\r\nConnection:\x20close\r\n\r\n\n<!DOCTYPE\x20html>\n<html>\n<he
SF:ad>\n\x20\x20\x20\x20<title>Love\x20Letters\x20Anonymous</title>\n\x20\
SF:x20\x20\x20<style>\n\x20\x20\x20\x20\x20\x20\x20\x20body\x20{\n\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20font-family:\x20'Georgia',\x20s
SF:erif;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20background:\x20l
SF:inear-gradient\(135deg,\x20#ff9a9e\x200%,\x20#fecfef\x20100%\);\n\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20min-height:\x20100vh;\n\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20display:\x20flex;\n\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20justify-content:\x20center;\n\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20align-items:\x20center;\n\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20margin:\x200;\n\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20padding:\x2020px;\n\x20\x20\x20\x
SF:20\x20\x20\x20\x20}\n\x20\x20\x20\x20\x20\x20\x20\x20\.container\x20{\n
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20background:\x20white;\n
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20padding:\x2040px;\n\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20border-radius:\x2020px;\n\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20box-shadow:\x200\x2010px\
SF:x2040px\x20rgba\(255,\x20105,\x20180,\x200\.3\);\n\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20\x20\x20\x20max-width:\x20600px;\n\x20\x20\x20\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20text-align:\x20center;\n\x20\x20\x20\x20\x20\
SF:x20\x20\x20}\n\x20\x20\x20\x20\x20\x20\x20\x20h1\x20{\n\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20color:\x20#ff1493;\n\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20margin-bottom:\x2020px")%r(RTSPRequest,1F4
SF:,"<!DOCTYPE\x20HTML\x20PUBLIC\x20\"-//W3C//DTD\x20HTML\x204\.01//EN\"\n
SF:\x20\x20\x20\x20\x20\x20\x20\x20\"http://www\.w3\.org/TR/html4/strict\.
SF:dtd\">\n<html>\n\x20\x20\x20\x20<head>\n\x20\x20\x20\x20\x20\x20\x20\x2
SF:0<meta\x20http-equiv=\"Content-Type\"\x20content=\"text/html;charset=ut
SF:f-8\">\n\x20\x20\x20\x20\x20\x20\x20\x20<title>Error\x20response</title
SF:>\n\x20\x20\x20\x20</head>\n\x20\x20\x20\x20<body>\n\x20\x20\x20\x20\x2
SF:0\x20\x20\x20<h1>Error\x20response</h1>\n\x20\x20\x20\x20\x20\x20\x20\x
SF:20<p>Error\x20code:\x20400</p>\n\x20\x20\x20\x20\x20\x20\x20\x20<p>Mess
SF:age:\x20Bad\x20request\x20version\x20\('RTSP/1\.0'\)\.</p>\n\x20\x20\x2
SF:0\x20\x20\x20\x20\x20<p>Error\x20code\x20explanation:\x20HTTPStatus\.BA
SF:D_REQUEST\x20-\x20Bad\x20request\x20syntax\x20or\x20unsupported\x20meth
SF:od\.</p>\n\x20\x20\x20\x20</body>\n</html>\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 95.85 seconds
gobuster dir -u http://<IP_Address>:5000 -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
gobuster dir -u http://<IP_Address>:5000 -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://<IP_Address>:5000
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,html,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/console (Status: 400) [Size: 167]
/robots.txt (Status: 200) [Size: 70]
/robots.txt (Status: 200) [Size: 70]
Progress: 18456 / 18460 (99.98%)
===============================================================
Finished
gobuster dir -u http://<IP_Address>:5000/cupids_secret_vault -w /usr/share/wordlists/dirb/common.txt -x php,html,txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://<IP_Address>:5000/cupids_secret_vault
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,html,txt
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/administrator (Status: 200) [Size: 2381]
Progress: 18456 / 18460 (99.98%)
===============================================================
Finished
===============================================================
curl -i http://<IP_Address>:5000
HTTP/1.1 200 OK
Server: Werkzeug/3.1.5 Python/3.10.12
Date: Sat, 14 Feb 2026 10:11:21 GMT
Content-Type: text/html; charset=utf-8
Content-Length: 1367
Connection: close
<!DOCTYPE html>
<html>
<body>
<div class="container">
<div class="heart">\u2764\ufe0f</div>
<h1>Love Letters Anonymous</h1>
<p>Welcome to our secret valentine message board!</p>
<p>Share your anonymous love letters with the world...</p>
</div>
</body>
curl -i http://<IP_Address>:5000/console
HTTP/1.1 400 BAD REQUEST
Server: Werkzeug/3.1.5 Python/3.10.12
Date: Sat, 14 Feb 2026 10:11:30 GMT
Content-Type: text/html; charset=utf-8
Content-Length: 167
Connection: close
<!doctype html>
<html lang=en>
<title>400 Bad Request</title>
<h1>Bad Request</h1>
<p>The browser (or proxy) sent a request that this server could not understand.</p>
curl -i http://<IP_Address>:5000/robots.txt
HTTP/1.1 200 OK
Server: Werkzeug/3.1.5 Python/3.10.12
Date: Sat, 14 Feb 2026 10:11:41 GMT
Content-Type: text/plain
Content-Length: 70
Connection: close
User-agent: *
Disallow: /cupids_secret_vault/*
# cupid_arrow_2026!!!
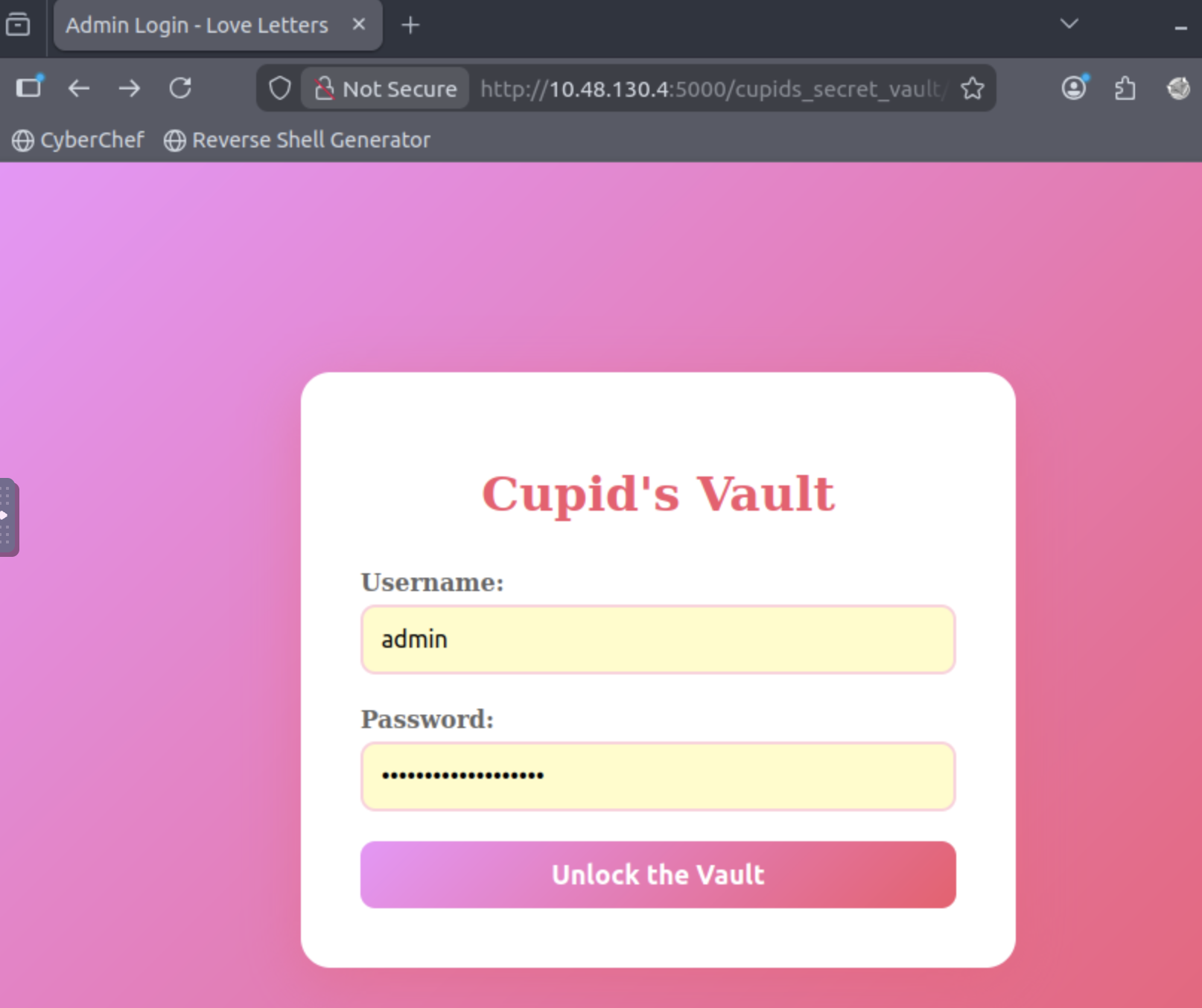
Visited the site: http://<IP_Address>:5000/cupids_secret_vault/administrator and used admin as the username and the password from the robots.txt file and ended finding the flag
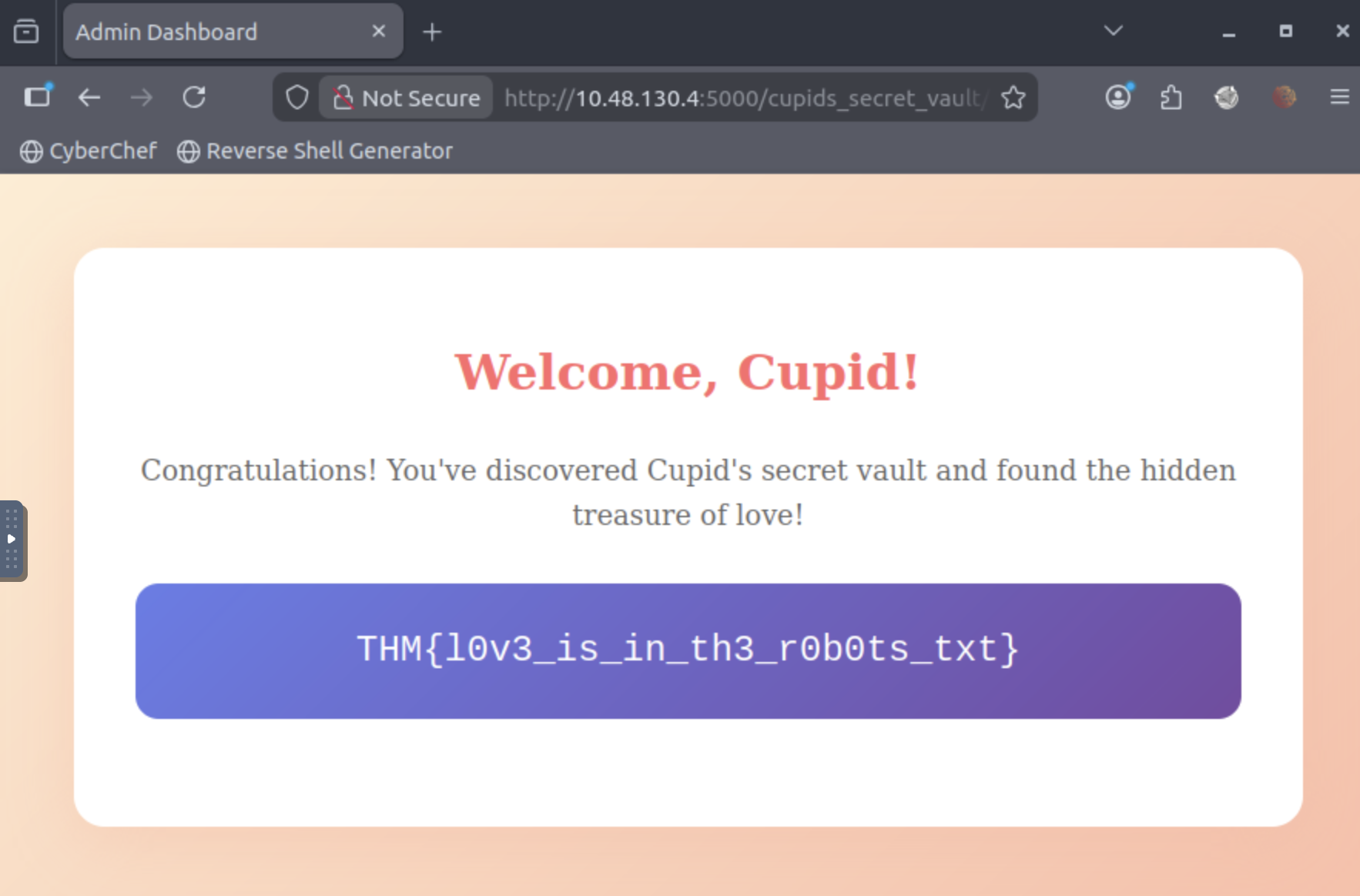
Lessons Learned
robots.txt is not a security measure - It's meant for web crawlers, not hiding sensitive paths
Never hardcode credentials - Especially not in comments or publicly accessible files
Enumeration is key - Systematic directory fuzzing revealed the admin panel
Default usernames - Always try common credentials like
admin,administrator,root
Tools Used
Nmap - Port scanning
Gobuster - Directory enumeration
curl - Manual HTTP requests




