Defensive Security: Digital Forensics Fundamentals (TryHackMe)
In this article, I will write a write-up for Digital Forensics Fundamentals that covers Introduction to Digital Forensics, Digital Forensics Methodology, Evidence Acquisition, and Windows Forensics.
Which team was handed the case by law enforcement?
digital forensicsWhich phase of digital forensics is concerned with correlating the collected data to draw any conclusions from it?
AnalysisWhich phase of digital forensics is concerned with extracting the data of interest from the collected evidence?
ExaminationWhich tool is used to ensure data integrity during the collection?
write blockerWhat is the name of the document that has all the details of the collected digital evidence?
chain of custodyWhich type of forensic image is taken to collect the volatile data from the operating system?
Memory ImageIf you take the above coordinates and search one of the online maps, you will learn more about this location. Searching Microsoft Bing Maps or Google Maps for
51 deg30' 51.90" N, 0 deg 5' 38.73" Wreveals the street where the photo was taken. Note that for the search to work, we had to replacedegwith°and remove the extra white space. In other words, we typed51°30'51.9"N 0°05'38.7"Win the map search bar.Using
pdfinfo, find out the author of the attached PDF file,ransom-letter.pdf.Ann Gree Shepherd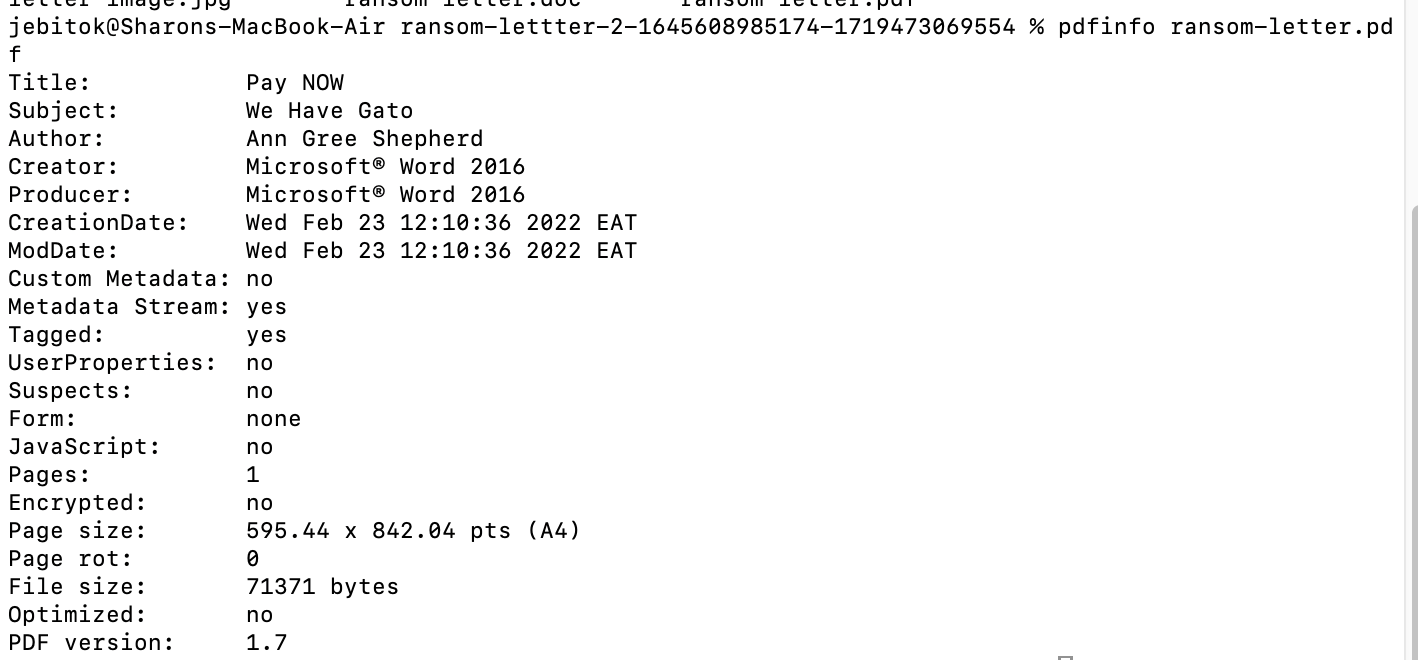
Using
exiftoolor any similar tool, try to find where the kidnappers took the image they attached to their document. What is the name of the street?Milk Street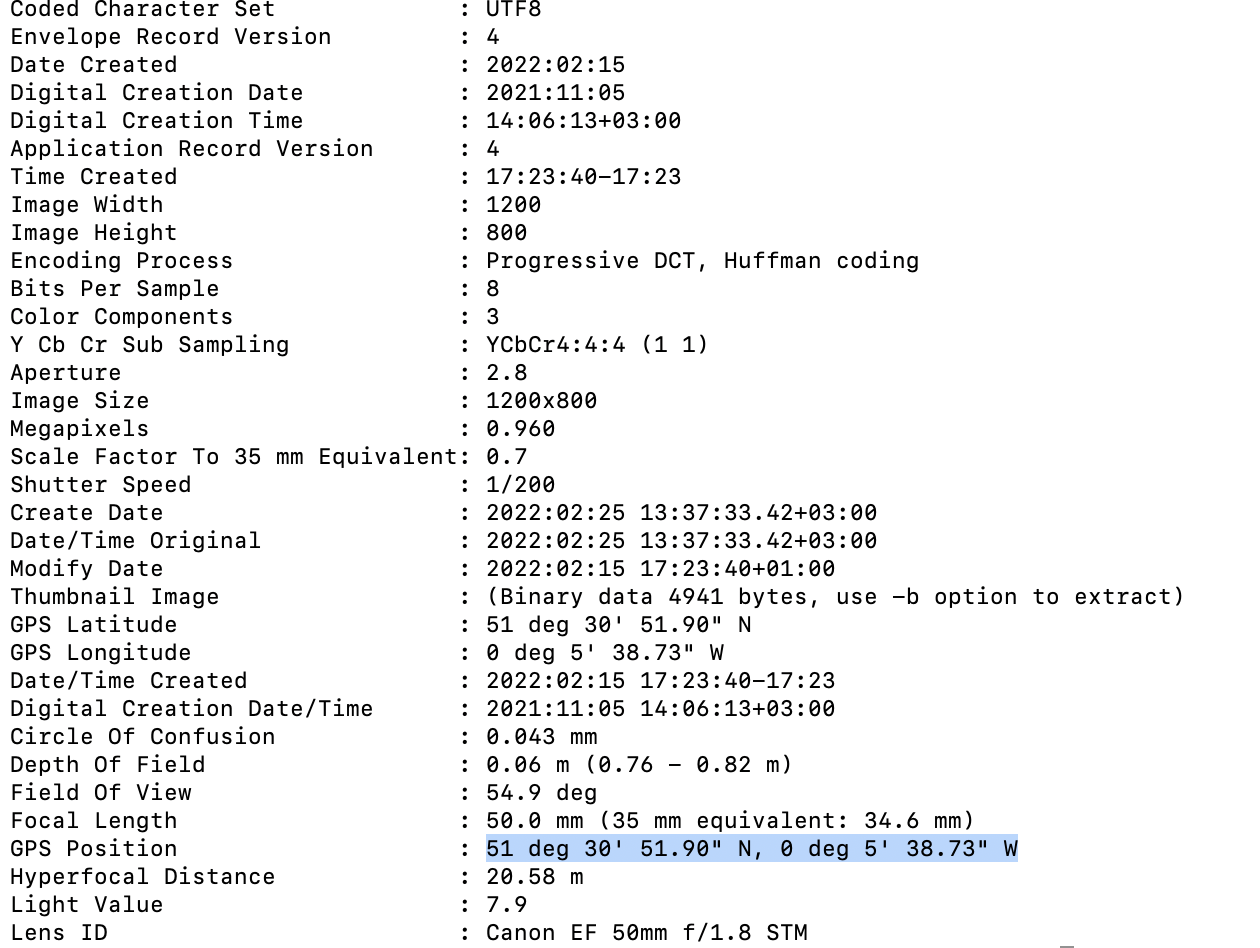
What is the model name of the camera used to take this photo?
Canon EOS R6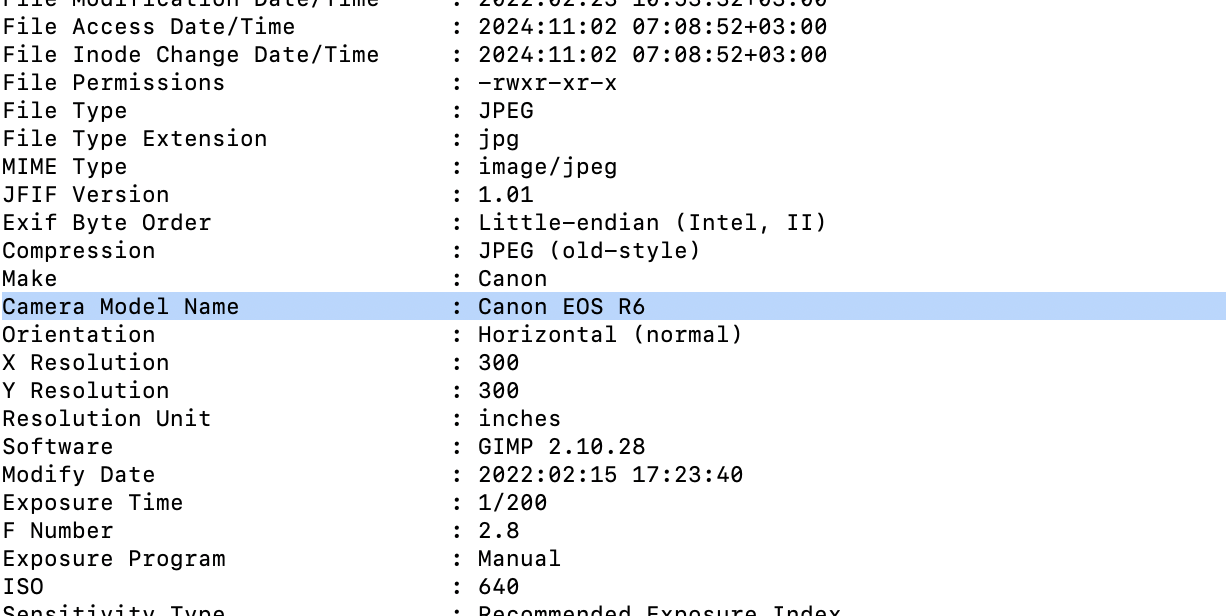
Thank you for reading my article. Please leave any questions or comments on improving my learning journey and the THM challenges.




